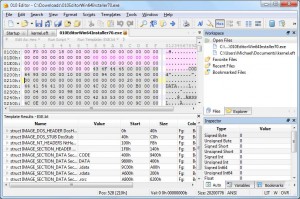
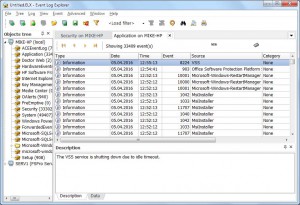
In the previous post we talked about 010 Editor, Event Log Explorer, ElcomSoft and Oxygen forensic solutions. In this blog post, we continue the brief review of prominent forensic tools.
Next on our list is Belkasoft.
Belkasoft Evidence Center 2016
Belkasoft Evidence Center is an all-around forensic solution to pinpoint, extract and review digital evidence stored on desktop computers, laptops and mobile devices.
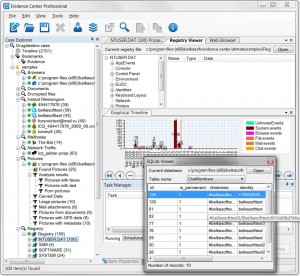 The Belkasoft product supports a wide range of devices. It can parse physical and logical drives, virtual machines, mobile device backups, JTAG, UFED images and chip-off dumps. Belkasoft Evidence Center performs an automated search for evidence and seamlessly identifies 700+ types of digital artifacts. Once the search is over, you can apply various filters for more granular results.
The Belkasoft product supports a wide range of devices. It can parse physical and logical drives, virtual machines, mobile device backups, JTAG, UFED images and chip-off dumps. Belkasoft Evidence Center performs an automated search for evidence and seamlessly identifies 700+ types of digital artifacts. Once the search is over, you can apply various filters for more granular results.
Belkasoft restores damaged or incomplete SQLite databases, and retrieves removed records and cleared history. It can glean crucial information from online chats and social networks, private browsing sessions, cleared browser history, cloud usage history, and more.
SQLite, Registry, and PList viewers enable the user to target specific data types and, ultimately, get more evidence than an automatic search would unveil. Other in-built analysis tools include File System Explorer, Hex Viewer and Type Converter for multi-aspect low-level examination of the content.
Belkasoft Evidence Center is deeply integrated with EnCase Version 7. This enables forensic investigators to obtain a multitude of evidence types supported by Evidence Center through the familiar EnCase interface. The integration is made possible with the free “BelkasoftDataImport” plugin.
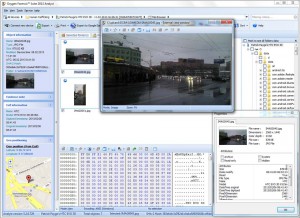
Rusolut’s Visual Nand Reconstructor
Rusolut is a manufacturer of Visual Nand Reconstructor (VNR), a comprehensive hardware and software data recovery and forensic analysis solution for damaged flash devices. The Reconstructor allows you to retrieve data from a multitude of Flash memory formats. The unique feature of Rusolut’s product is the ability to automate data structure recognition and dramatically speed up the recovery process.
 The embedded base of NAND chips and controller configurations caters to most known chips. The database is subject to regular updates by the Rusolut team and their tech partners. A built-in file system viewer operates with the most commonly used file systems – FAT and NTFS.
The embedded base of NAND chips and controller configurations caters to most known chips. The database is subject to regular updates by the Rusolut team and their tech partners. A built-in file system viewer operates with the most commonly used file systems – FAT and NTFS.
VNR makes reverse engineering easy with special modes of data visualization and multi-tier descriptions of image structure. The special scrambler extraction mode enables successful data decryption even with new devices.
Despite its complex functionality, VNR offers a user-friendly interface with unified controls to help restore and analyze data in a more efficient manner. These include automatic analysis features that facilitate image reconstruction and data recovery. Check out the elaborate documentation to see if your investigation finds the right solution with Rusolut.
Passware Kit Forensic
Passware focuses on password recovery and caters to numerous use cases. Its Kit Forensic is a comprehensive evidence discovery solution that detects and decrypts all password-protected items on a computer.
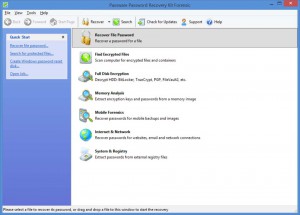 Passware helps to recover or reset passwords for 200+ document types, including Windows, Word, Excel, QuickBooks, Access, Acrobat, etc. Kit Forensic scans for encrypted evidence, and performs live memory analysis and batch processing.The software works smoothly with BitLocker, TrueCrypt, FileVault2 and PGP; it supports GPU, TACC, Distributed Computing, and Rainbow Tables. Kit Forensics integrates easily with Guidance EnCase v7 in case the user needs to match collected data across two systems.
Passware helps to recover or reset passwords for 200+ document types, including Windows, Word, Excel, QuickBooks, Access, Acrobat, etc. Kit Forensic scans for encrypted evidence, and performs live memory analysis and batch processing.The software works smoothly with BitLocker, TrueCrypt, FileVault2 and PGP; it supports GPU, TACC, Distributed Computing, and Rainbow Tables. Kit Forensics integrates easily with Guidance EnCase v7 in case the user needs to match collected data across two systems.
Check out the references and learn how Passware tools have resolved real situations; for instance, their operations on cracking otherwise undecipherable passwords in child pornography cases. In those projects, Passware helped investigators from the Swedish and US police forces with equally successful results.
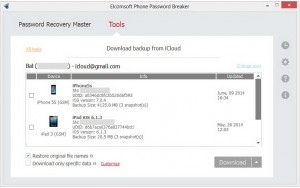
Passcovery
Passcovery Co. Ltd. offers forensics, corporate and home users performance-driven password recovery.
Their flagship Passcovery  Suite successfully operates with Microsoft Office, OpenOffice, PDF, ZIP/RAR, iOS/Blackberry back-ups, TrueCrypt volumes and WPA/WPA2 handshakes. The Suite uses an embedded macro language for sophisticated password generation assignments. The key focus of Passcovery is fast retrieval of data. The software boasts great recovery speeds, as well as optimization for AMD/ATI and NVIDIA video cards. Passcovery detects your CPU type and operates accordingly to deliver optimal performance. Whenever possible, it employs GPU password recovery with AMD and NVIDIA video cards.
Suite successfully operates with Microsoft Office, OpenOffice, PDF, ZIP/RAR, iOS/Blackberry back-ups, TrueCrypt volumes and WPA/WPA2 handshakes. The Suite uses an embedded macro language for sophisticated password generation assignments. The key focus of Passcovery is fast retrieval of data. The software boasts great recovery speeds, as well as optimization for AMD/ATI and NVIDIA video cards. Passcovery detects your CPU type and operates accordingly to deliver optimal performance. Whenever possible, it employs GPU password recovery with AMD and NVIDIA video cards.
Plus, Passcovery can leverage multiple video cards at the same time.
PasswordLastic
PasswordLastic is another password retrieval solution focused on Microsoft Windows and Office products.
The tool offers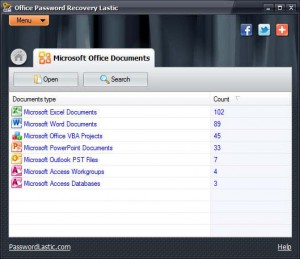 an online password cracking service that helps to crack Word and Excel documents in no time. Office Password Recovery Lastic supports MS Word, Excel, PowerPoint, Outlook and Access files, as well as embedded VBA projects.
an online password cracking service that helps to crack Word and Excel documents in no time. Office Password Recovery Lastic supports MS Word, Excel, PowerPoint, Outlook and Access files, as well as embedded VBA projects.
Windows Password Recovery Lastic helps to restore access to the operating system. Run the software on an available computer and create a bootable USB stick or CD/DVD. Boot from it on the required computer and reset the password for any of the previous accounts. Plus, the program saves password hashes for in-depth cracking and recovery of previously removed passwords.
Other standalone versions cater to Outlook, Excel, Word and VBA projects. Easy-to-use and effective tool for average users and forensic experts alike.
Bottom line
If you are interested in professional forensic tools, make sure you research the market. Digital forensics is entering a golden era in terms of technology, and the offering is abundant, so define your goals and budget first, then determine which one addresses your particular investigative needs.